BLOG
Mary Marquardt: Unveiling the Woman Beyond the Spotlight

Mary Marquardt is a mysterious woman despite her notable achievements; her name is recognized to those who are knowledgeable with Hollywood’s past. Throughout her life, Mary has demonstrated strength, originality, and development, from her humble beginnings to the lasting influence she has had on popular culture.
Early Life
The early years of Mary’s childhood were impacted by a variety of factors due to her multicultural family. Coming from a family that placed a premium on education, she set out on a quest that would take her down hitherto uncharted roads.
Marriage to Harrison Ford
Marriage to the renowned Harrison Ford is an integral part of Mary Marquardt’s story. How they met, the intricacies of their relationship, and how the public saw this power couple are all parts of the story that we uncover.
Professional Achievements
Mary Marquardt was an accomplished professional in addition to her function as a wife. Here we take a look at her career highlights, including the major accomplishments that made her stand out.
Life Beyond Marriage
Although Mary’s marriage to Harrison Ford was a watershed moment in her life, the divorce was just the beginning. What she did after her divorce and how it shaped her into the woman she is now are topics we cover.
Family and Personal Life
Above and beyond her glamorous persona, Mary Marquardt was a dedicated mother and person. She has depth to her character because of her family, which we examine in greater detail along with her children and hobbies.
Public Persona
Mary Marquardt experienced the highs and lows of fame. The media’s portrayal of her and her efforts to control her public image are examined.
Legacy
The impact of Mary Marquardt goes far beyond her work in Hollywood. In this section, we will explore her lasting legacy by looking at how she influenced the industry and the stories told in popular culture.
Reflections and Interviews
The interviewee Mary allows us to see the real person behind the famous by sharing her thoughts and experiences. Her introspections offer a rare window into her mind and life.
Challenges Faced
There will be obstacles on every trip. Here we delve into Mary Marquardt’s personal and professional struggles, as well as her triumphs over them.
Cultural Significance
Cultural narratives were significantly influenced by Mary Marquardt. In this article, we will explore her impact on diversity and inclusion in Hollywood.
Social Media Presence
Mary Marquardt’s online presence continues to make an impression, even in this digital age. We look at how her participation in social media affected her lasting legacy.
Fanbase and Community
Mary’s loyal following is still strong. This section delves into her devoted fan base and any community service she could have done.
Enduring Impact
In closing our exploration, we consider the reasons Mary Marquardt is still relevant and the impact she will have on generations to come, guaranteeing that her legacy will endure.
Conclusion
A story of progress, innovation, and perseverance is Mary Marquardt’s life story. She has had an everlasting impression on the entertainment world, from her early days to her enduring legacy.
FAQ’s
Did Mary Marquardt continue working in the entertainment industry after her divorce from Harrison Ford?
Following her divorce, Mary Marquardt sought for opportunities outside of the entertainment sector and embarked on new projects.
How did the media portray Mary Marquardt during her marriage to Harrison Ford?
The media’s portrayal of the power couple was mixed, with some outlets praising them and others attacking them.
What challenges did Mary Marquardt face in her personal and professional life?
Mary overcame challenges in her personal and professional lives by staying strong and focused.
How has Mary Marquardt’s legacy impacted future generations in Hollywood?
The way people of all ages approach the complex entertainment industry is influenced by Mary’s lasting legacy.
BLOG
Wellozgalgoen – Learn Everything About This Platform
Introduction
Wellozgalgoen is an unusual and uncommon term that appears like a platform name, but there is no verified or widely recognized software, company, or digital service officially associated with it. Instead, it is best understood as a synthetic or emerging digital keyword that resembles a platform-style branding name.
Because of its structure, it often appears in discussions around SEO experiments, digital identity concepts, or placeholder platform naming.
What Is Wellozgalgoen?
Wellozgalgoen can be described as:
- A fictional or placeholder platform name
- A SEO-generated or experimental keyword
- A digital identity-style term used in content testing
- A name that mimics SaaS or tech platform branding
In simple terms, it is a constructed name that looks like a platform but has no confirmed real-world system behind it.
Why Names Like Wellozgalgoen Exist
1. SEO and Content Testing
Marketers and content creators sometimes use unique terms like this to:
- Test how search engines index new keywords
- Analyze ranking behavior without competition
- Track visibility of fresh content
Because the keyword is unique, it becomes useful for controlled SEO experiments.
2. Placeholder Branding
Developers and creators often invent names like Wellozgalgoen when:
- Building mockups or prototypes
- Designing UI/UX concepts
- Testing product naming ideas
It acts as a temporary brand identity before real naming decisions.
3. Database or System Simulation
In technical environments, random platform-like names may be used for:
- Dummy data
- System simulations
- API testing environments
4. Digital Trend Formation
Sometimes, unusual names become semi-trending due to:
- Curiosity searches
- Blog content repetition
- Algorithm-driven indexing
This can make them appear more “real” than they actually are.
Key Features (Conceptual Interpretation)
Since Wellozgalgoen is not an official platform, its “features” are hypothetical based on how such names are typically structured.
1. Platform-Like Branding
- Sounds like a SaaS or tech service
- Structured like modern digital product names
2. High Uniqueness
- No known duplicates in major systems
- Ideal for branding experiments
3. SEO Flexibility
- No competition in search engines
- Easy to rank content using the keyword
4. Adaptability
- Could theoretically be used for any digital product
- Suitable for apps, tools, or services if ever developed
Possible Interpretations
People may interpret Wellozgalgoen in different ways:
1. Future Tech Platform
It could sound like:
- A cloud service
- A software platform
- A digital productivity tool
2. Experimental Project Name
Used in:
- Internal development
- Startup idea testing
- Concept demonstrations
3. SEO Placeholder Term
Used purely for:
- Ranking experiments
- Content indexing tests
- Keyword tracking
Is Wellozgalgoen a Real Platform?
No. There is:
- ❌ No verified software or app
- ❌ No official company or service
- ❌ No documented product functionality
It exists only as a constructed or conceptual keyword.
Is It Safe?
Yes, the term itself is harmless.
However, caution is needed if it appears in:
- Unknown download links
- Suspicious websites claiming “access”
- Fake apps using the name
The risk lies in misuse, not the word itself.
Why It Feels Like a Real Platform
Wellozgalgoen sounds convincing because:
- It follows modern tech naming patterns
- It resembles SaaS platform branding
- It appears structured and complex
- It fits digital product naming trends
This makes it feel legitimate even when it is not.
Final Thoughts
Wellozgalgoen is not a real platform—it is a synthetic, platform-like keyword used in SEO, branding experiments, or conceptual digital naming.
Its importance comes from how it demonstrates:
- Modern naming trends in tech
- The power of SEO-driven curiosity
- How easily digital identities can be created
In today’s internet ecosystem, even invented names can appear meaningful when repeated and indexed online.
FAQ’s
What is Wellozgalgoen?
It is a synthetic or placeholder platform-style keyword with no confirmed real-world service behind it.
Is Wellozgalgoen a real app?
No, there is no verified app or software with this name.
Why does it look like a tech platform?
Because it is structured to resemble modern SaaS or digital product naming conventions.
Is it used in SEO?
Yes, such unique terms are often used in SEO testing and experiments.
Is Wellozgalgoen safe?
The term itself is safe, but always be cautious of unknown links using it.
BLOG
Techehla.com: Your Hub for Technology Updates and Reviews
Introduction
Techehla.com is typically presented as a tech-focused online platform that covers technology news, gadget reviews, software insights, and digital trends. Sites with this kind of branding usually aim to simplify complex tech topics for everyday readers while also offering updates on the latest innovations.
Whether it is a blog, content hub, or review site, the idea behind Techehla.com is centered on making technology information accessible, practical, and easy to understand.
What Is Techehla.com?
Techehla.com can be described as a technology information and review website concept that focuses on:
- Tech news and updates
- Product and gadget reviews
- Software and app insights
- How-to guides and tutorials
- Digital trends and innovations
In simple terms, it acts as a central hub for tech-related knowledge and updates.
Key Features of Techehla.com
1. Technology News Coverage
One of the main features is providing updates on:
- New smartphone launches
- Software updates
- AI and emerging technologies
- Tech industry trends
This helps users stay informed about the fast-changing digital world.
2. Product Reviews
Techehla-style platforms often publish reviews on:
- Mobile phones
- Laptops and computers
- Smart devices (wearables, home gadgets)
- Software tools and apps
Reviews usually focus on performance, usability, and value for money.
3. How-To Guides
Another important feature includes step-by-step tutorials such as:
- Setting up devices
- Using software tools
- Fixing common tech issues
- Optimizing system performance
These guides are designed for beginners and non-technical users.
4. Software and App Insights
Techehla.com may also cover:
- Productivity apps
- AI tools
- Security software
- Editing and design tools
This helps users choose the right tools for their needs.
5. Tech Comparisons
Comparison articles often include:
- Android vs iOS devices
- Laptop vs tablet performance
- Software tool alternatives
These comparisons help users make informed decisions.
Benefits of Techehla.com
1. Easy Access to Tech Knowledge
It simplifies complex topics so that even beginners can understand technology.
2. Time-Saving Information
Instead of searching multiple sources, users get summarized insights in one place.
3. Helps in Buying Decisions
Reviews and comparisons guide users before purchasing gadgets or software.
4. Keeps Users Updated
Regular updates help readers stay informed about new technologies and trends.
5. Beginner-Friendly Learning
Content is often structured in a way that is easy to follow, even for non-experts.
Why Tech Review Sites Like Techehla.com Are Popular
Platforms like Techehla.com gain popularity because:
- Technology is constantly evolving
- Users want trusted reviews before buying products
- People prefer simplified explanations
- Online learning and tech awareness are increasing
How to Evaluate Tech Websites Safely
If you are using any tech review site, consider:
- Checking credibility of sources
- Comparing reviews with other platforms
- Looking for real user feedback
- Avoiding exaggerated claims
This ensures you make reliable and informed decisions.
Final Thoughts
Techehla.com represents a modern tech information hub concept focused on delivering updates, reviews, and guides in a simple and accessible way. Whether it is real or emerging as a digital content platform, its purpose aligns with the growing demand for clear, practical, and updated technology knowledge.
FAQ’s
What is Techehla.com?
It is a tech-focused platform concept offering news, reviews, and digital guides.
Is Techehla.com a real tech news website?
It is generally presented as a tech content hub, though availability and structure may vary.
What type of content does it provide?
Tech news, product reviews, software insights, and tutorials.
Is it useful for beginners?
Yes, it is designed to simplify complex technology topics.
Can I trust tech review sites like Techehla.com?
They can be useful, but it’s always best to compare information with multiple sources.
BLOG
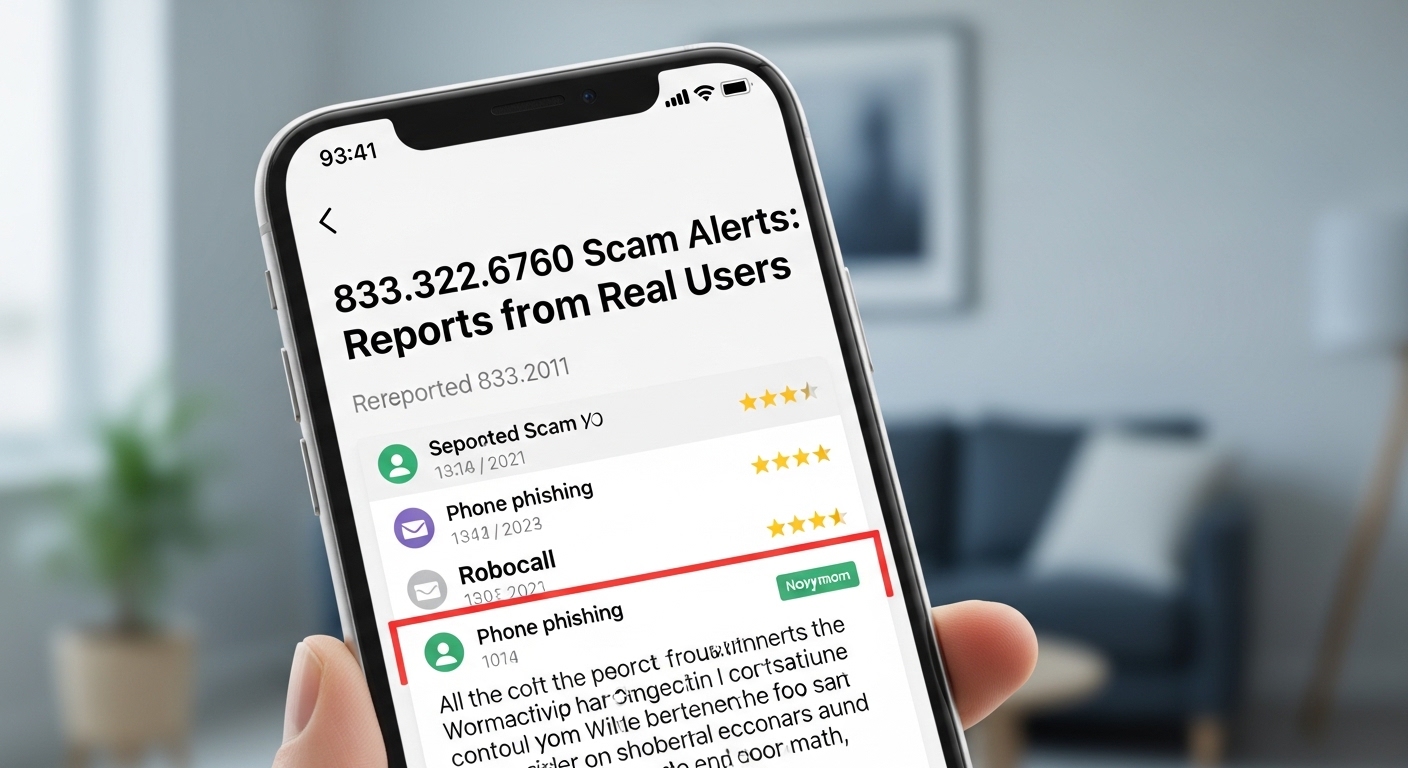
833.322.6760 Scam Alerts: Reports from Real Users
Overview
If you’ve been getting calls from 833.322.6760, you’re not alone. Many people report repeated calls, vague voicemail messages, and high-pressure scripts that try to extract personal or financial information. In this guide, I’ll break down the most common patterns associated with this number, how to recognize red flags quickly, and practical steps to protect yourself and report the behavior. I’ll also share a sensible response playbook you can follow when any unknown number rings—because the number may change, but the tactics often don’t.
What Is 833.322.6760?
Toll-free numbers using the 833 prefix are commonly used by legitimate businesses, nonprofits, and government hotlines. However, scammers also exploit toll-free ranges because they can cycle numbers easily and mask their identity. Reports around 833.322.6760 suggest behavior consistent with lead-generation robocalls and debt- or account-related phishing attempts. While a single number can be spoofed (faked caller ID), the patterns and scripts tend to be similar across many such campaigns.
Why This Number Appears Frequently
- Call centers can automate large call volumes and rotate through regional time zones
- Spoofing technology allows callers to reuse or imitate the same number across campaigns
- Public data breaches and data brokers fuel targeted lists that keep phones ringing
Common Call Patterns and Scripts
“Urgent Account Issue” or “Suspicious Activity”
Callers claim there’s a lock, hold, or unusual activity on your bank, credit card, or e-commerce account. They’ll push you to “verify” details—full name, date of birth, card digits, or one-time codes. Legitimate institutions rarely demand sensitive details via inbound calls and always support secure callbacks via official channels.
“Debt or Collection Notice”
You might hear that you owe a past-due balance, face legal action, or must settle immediately to avoid escalation. High-pressure tactics, threats, or refusal to provide written validation are hallmark signs of scams. If it’s a real collection effort, you have rights under the Fair Debt Collection Practices Act (FDCPA) in the U.S., including the right to request written verification.
“Warranty and Benefits Upsells”
These scripts push extended auto warranties, medical benefit cards, or home-protection plans. The offer sounds time-limited and urgent. If asked to pay upfront or to share banking info to “activate benefits,” hang up and research independently.
“Tech Support or Device Compromise”
Sometimes the caller says your computer or phone is infected and needs immediate remote access or a service fee. Real vendors don’t call out of the blue to fix your device; tech-support scams rely on fear and fast compliance.
Red Flags to Spot Instantly
- Requests for personal data: SSN, full DOB, full card numbers, or one-time passcodes
- Payment demands via gift cards, crypto, or wire transfer
- Refusal to identify the company or provide a verifiable callback number
- Caller ID mismatch with the claimed organization
- Threats (arrest, lawsuits, account closure) or extreme urgency
- Poor audio quality, background call-center chatter, or scripted responses
How to Respond Safely
Step 1: Don’t Engage With Sensitive Info
Never share personal or financial details with an unsolicited caller. If the claim sounds plausible, end the call politely and use an official number (from a bank card, website you typed directly, or your account app) to verify.
Step 2: Block and Filter
- Use your phone’s built-in block and spam-label features
- Enable carrier-level spam filtering (most major carriers offer this)
- Consider reputable third-party call-screening apps that crowdsource reports
Step 3: Document and Report
- Save the date/time, the number displayed, and any requested information
- File a report with the FTC (U.S.) or your country’s consumer protection agency
- If threats or impersonation of government agencies occur, report to appropriate authorities
- Inform your bank or credit card issuer if you shared any details by mistake
Step 4: Guard Your Accounts
- Change passwords and enable multi-factor authentication (MFA) on critical accounts
- Review recent transactions and set up real-time alerts
- Consider a credit freeze or fraud alert with major bureaus if sensitive info was exposed
Verification Tactics That Work
Call Back Using Official Channels
If the caller claims to represent your bank or a familiar service, hang up and dial a number you trust—printed on your card, statement, or the organization’s website (not a link sent by text or email). A legitimate agent can confirm whether contact was attempted.
Ask for Written Validation
For any debt-related call, request written validation via mail. Real collectors are legally required to provide this. Refusal or pushback signals a likely scam.
Control the Pace
Scammers rely on panic. Slow the conversation, insist on details, and take notes. If the caller becomes aggressive, that’s your cue to disconnect.
What If You Already Shared Information?
- Financial data (card, bank): Contact your bank immediately, lock or replace the card, and dispute any unauthorized charges
- Account credentials: Change passwords and revoke any active sessions; turn on MFA
- SSN or sensitive ID: Consider a credit freeze, monitor reports, and watch for new-account alerts
- Remote access granted: Disconnect the device from the internet, run reputable security scans, and consider a professional checkup
Why These Calls Persist
Economics of Robocalling
It’s cheap to dial thousands of numbers per minute. Even a tiny success rate can be profitable, which keeps bad actors in business.
Data Availability
Large-scale breaches and public data trades fuel targeted lists. Attackers can personalize scripts just enough to sound believable.
Enforcement Challenges
International operations, spoofing tactics, and fast-moving campaigns make enforcement difficult. Still, reporting helps investigators map patterns and shut down infrastructure.
Building a Personal Defense Plan
Harden Your Personal Info
- Use unique, strong passwords and a password manager
- Enable MFA wherever possible
- Limit the personal details you share publicly
Train Your Reflexes
- Let unknown calls go to voicemail
- Treat urgency as a red flag
- Verify through official channels, not the number that called you
Keep Family in the Loop
- Share these tactics with family members, especially teens and older adults
- Create a household “verification code” for money or help requests
- Encourage a callback rule: hang up and call back using verified numbers
Frequently Asked Questions
Is 833.322.6760 always a scam?
No single number is inherently always a scam, especially with spoofing in play. What matters are the behaviors. Use the verification steps and never rely solely on caller ID.
Can I stop these calls completely?
You can reduce them significantly with carrier filters, blocklists, and call-screening apps, but total elimination is unlikely. Consistent blocking and reporting help over time.
Should I call back the number?
It’s safer to avoid calling back unknown numbers. If the message claims to be from a known institution, call that institution directly using an official number you locate yourself.
The Bottom Line
Unwanted calls from numbers like 833.322.6760 thrive on pressure and confusion. By recognizing common scripts, slowing down the interaction, and verifying through trusted channels, you flip the script. Protect your information, report suspicious activity, and keep your accounts locked down. A calm, methodical response is your best defense.
-

 TECH1 month ago
TECH1 month agoOlxking123.com: How is Revolutionizing the Online Bargain Industry
-
 BLOG1 month ago
BLOG1 month agoOnulife: Your Ultimate Guide to a Healthier & Balanced Lifestyle
-

 TECH1 month ago
TECH1 month agoDeshoptec.com: The Ultimate Marketplace for Cutting-Edge Tech
-

 BLOG1 month ago
BLOG1 month agoExploring Gooics: Features, Benefits, and How It Works Now
-

 HOME1 month ago
HOME1 month agoTopHillSport.com: A Growing Hub for Sports Enthusiasts
-

 BLOG1 month ago
BLOG1 month agoWhy Runlia is the Next Big Thing in Online Communities
-

 BLOG1 month ago
BLOG1 month agoChromiumFX: Advanced Analytics and AI for Smart Systems
-

 BLOG1 month ago
BLOG1 month agoCintia Coció: The Ultimate Guide to Her Modern Culinary World
